12 Things you should know about Keyloggers
2015-10-16
A keylogger is a piece of software or hardware which records user activities: keystrokes, mouse movements and clicks, etc.Thing 1
Keylogger’s main idea and goal is to intervene the signal circuit from the key pressing to displaying it on the screen. There can be hardware “bugs” in the keyboard itself, in the cable or in computer system unit, video surveillance, input-output requests interception, substitution of system keyboard driver, driver-filters ion keyboard stack, kernel functions interception by any method (changing addresses in system tables, function code splicing, etc), DLL functions interception in user mode and, finally, keyboard inquiry using typical documented way.
Thing 2
But practice shows that the more difficult method is used the less likely it will be used as a widespread Trojan malware. But it is more likely to be used in target Trojans to steal corporate, personal, financial and confidential information.

Thing 3
Types of information that can be controlled
- keystrokes
- mouse movement and clicks
- date and time of pressing
Additionally, there can be screenshots (sometimes – screen video) and data copying from the clipboard.
Classification
Thing 4
By type
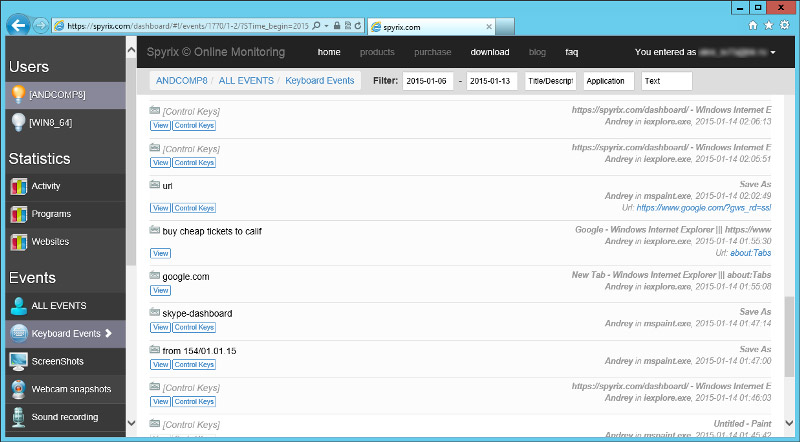
Program keyloggers belong to the group of software products that control user activity on PC. Initially, software products of this type were intended solely for recording information about keystrokes, including system ones to a special log file that would later be studied by a person who installed this program. Log file could be sent to a network disc, FTP-server on the Internet, via email, etc.
Nowadays software products which retained this name, perform many additional functions – interception of windows data, mouse clicks, clipboard, making screenshots of the screen and active windows, keeping records of all received and sent emails, monitoring files activity and work with system registry, record tasks sent to the printer, interception of sound from the microphone and video from the webcam, etc.
Hardware keyloggers are miniature devices that can be installed between within the keyboard-computer connection or inside the keyboard. They record all keystrokes from the keyboard. The recording process is absolutely invisible for the end user. Hardware keyloggers do not require any applications installed on the computer to successfully intercept all keystrokes. When a hardware keylogger is connected it does not matter whether the computer is turned on or off.

Time of a hardware keylogger's work is not limited, as it does not require an additional power source for its operation. The internal memory capacity of such devices allows recording up to 20 million keystrokes with Unicode support.
These devices can be made in any form factor so that even an expert sometimes is unable to determine their presence during an inspection.
Depending on the place of installation, keyloggers are divided into internal and external.
Acoustic keyloggers are hardware devices which first record sounds, created by the user while pressing keyboard keys and then analyze these sounds and convert them into the text format
Thing 5
By the log-file storage location
- HDD
- RAM
- registry
- local network
- remote server
- a cloud-based platform. The best and most popular keylogger program is Spyrix Keylogger, you can read more about it here
Thing 6
By log file sending method
- FTP or HTTP (via the Internet or local network)
- Any variant of wireless connection (radio band, IrDA, Bluetooth, WiFI, and other variants for devices in immediate proximity or in advanced systems, to overcome the air gap and data leakage from physically isolated systems)
Thing 7
By the method of usage
Only the method of keylogger usage (including hardware and software products with a keylogger as a module) allows seeing the distinction between security control and security violation.
- Unauthorized use – keylogger's installation (including hardware or software products with a keylogger as a module) takes place without the knowledge of the automated system owner (security administrator) or the owner of a particular PC.
Unauthorized keyloggers (software or hardware) are called spyware or spy gadgets.
Unauthorized use is usually associated with illegal activities. Generally, illegally installed spyware have the ability of configuration and obtaining ready executable files that do not display any messages and do not create windows on the screen during installation. They also have built-in resources for delivery and remote installation of a pre-configured module on the user’s computer, so that the installation process takes place without direct physical access to the user’s PC and often does not require system administrator rights.
- Authorized use – keylogger installation (including hardware or software products with a keylogger as a module) takes place with the knowledge of the automated system owner (security administrator) or the owner of a particular PC.
Generally, the legally installed software requires physical access to the PC and administrator rights for configuration and installation.
Thing 8
By included signature bases
Signatures of known keyloggers are already included to the signature bases of famous antispyware and antivirus software developers.
Unknown keyloggers, that do not have their signatures in bases, are often never included there for various reasons:
- keyloggers (modules) that are developed under the protection of various government agencies;
- keyloggers (modules) that can be created by the developers of various closed-source operating systems and be included in the system’s kernel.
- keyloggers that are developed in limited edition (often in one or several copies) for a particular purpose related to the theft of critical information from some PC (e.g. software used by professional frauds). Such spyware may imply a bit changed open-source codes of keyloggers, taken from the Internet, and be compiled by a fraud himself, that allows changing a keylogger‘s signature;
- commercial keyloggers, especially the ones that are included as modules in corporate software, are rarely added to the signature bases of famous antispyware and antivirus software developers. This leads to the situation when the fully functional version of the software published by a fraud on the Internet is converted to the spyware which is not detected by antispyware and antivirus software;
- keyloggers as modules included in virus applications for keystrokes interception on the user’s computer. Before including signature data in virus database these modules remain unknown. As an example a well-known virus that caused much trouble recently, which had a module of keystrokes interception and was sending the recorded data via the Internet.
The purpose of use
Thing 9
The authorized use of keyloggers (including hardware or software products with a keylogger as a module) allows the automated system owner (security administrator) or the owner of a particular PC the following:
- identifying all cases of typing critical words and phrases that will result in property damage when transferred to third parties;
- a possibility of getting access to the information on the computer’s hard drive in case of login and password loss for any reason (employee illness, intentional actions of staff members, etc);
- identifying (locating) all attempts of passwords searching;
- controlling a possibility of using computers in free time and finding out what was typed on the keyboard during this period;
- investigating computer incidents;
- carrying out scientific researches related to the determination of staff response accuracy, efficiency and resilience against external impacts;
- restoring critical information after computer systems failure.
Using modules with a keylogger allows developers of commercial software:
- creating systems of quick words search (electronic dictionaries, electronic translators);
- creating applications for quick search of names, organizations, addresses (electronic phone books).
Unauthorized use of keyloggers (including hardware or software products with a keylogger as a module) allows a fraud:
- intercepting information typed on the keyboard by the user;
- getting unauthorized access to login information for various systems including bank-client type systems;
- getting unauthorized access to the systems of user data cryptographic protection – password phrases;
- getting unauthorized access to credit cards information.
Keylogger principles
Thing 10
A standard keyboard trap
Generally, there are enormous variants of keylogger implementing; however, all of them have one common principle of work - penetration of the signal chain between the key pressing to displaying it on the screen. The most common variant of implementation is a keylogger with a keyboard trap. Keyboard hooks read information from a system queue of hardware input that is in the csrss.exe system process.
This method gained particular popularity due to the fact that a filter trap allows intercepting absolutely all keystrokes because the hook controls all system flows. Also, such spyware creation does not require any special knowledge, except Visual C++ or Delphi and Win32API. However, such method requires creating DLL dynamic library.
Recurring keyboard status inquiry
A primitive method implying a cyclic keyboard status inquiry at a high speed. Such method does not require implementation of DLL in GUI-processes and, as a result, a spyware is less noticeable.
The disadvantage of this type of keyloggers is the need of recurring keyboard status inquiry at a high speed, at least 10-20 inquiries per second. This method is used by several commercial products.
Driver-based keylogger
This method is more effective in comparison with the above-mentioned one. There are at least two ways of implementing this method: creation and installation of a special keyboard driver instead of the standard one or installation of a driver-filter. This method (as well as a trap) is a documented method of keystrokes tracking.
Thing 11
Spy-rootkit
Can be realized both in UserMode and in a KernelMode. In UserMode keyboard input tracking can be done in the csrss.exe process by intercepting of keyboard driver or tracking of API-functions like GetMessage and PeekMessage. In many cases, even the on-screen keyboard, which is often considered a panacea from any keylogger, does not protect from the rootkit-keylogger.
Hardware keyloggers
Thing 12
To search for keyloggers on your home computer it is enough to be sure in the absence of keylogger applications. However, in a corporate environment, in particular on computers for bank transactions, electronic trading, and for performing tasks associated with the processing of confidential documents, there is a risk of the hardware for keystrokes interception being present.
Let’s have a look at the main channels of information leakage in terms of the hardware.
1. A hardware insert in the keyboard
In any keyboard there are usually lots of cavities with the size enough for placing a small board in. Device power and data transferring can be done by direct connection to the printed circuit card of a keyboard controller. Hardware tab can be installed manually or by the manufacturer.
Solution: keyboard opening and checking for the presence of unrelated electronic components with the further keyboard sealing using.
2. Reading data from the keyboard cable by contactless method
This method implies data reading by a contactless sensor. Such device installation does not require keyboard opening and mounting any equipment in the cable gap. Contactless hardware keylogger should be self-powered and its construction supposed to be more complex than in case of direct connection. Such a device may look like a removable noise filter for the cable.
Solution: contactless reading is the most effective method when placing the sensor in the close proximity to the keyboard cable (or even better – around the cable), that is why, when inspecting work places, make sure that there are no foreign objects of unknown purpose near the keyboard cable or directly on it.
3. Device installation between the cable and the PC
Keyloggers of this type are the most common ones, they are easy to be installed and detected. A hardware keylogger, in this case, looks like a small device, which is inserted in the PS/2- or USB port of the computer and a keyboard is inserted into the socket in the keylogger. To perform such an operation no skill is required, and besides, keylogger connection to the USB- keyboard can be done without shutting down the computer.
Hardware keylogger may look like a noise filter or adapter. The device consists of the input circuits intended to filter noise and protect the device against over-voltage, a microcontroller with a low power consumption, and Flash-memory for storing the collected information. Flash-memory volume varies from 32 KB to dozens of megabytes; the typical amount is from 128 KB to 2 MB.
Solution: periodic inspection of the workplace for the presence of unauthorized devices inserted in the keyboard cable socket. The keyboard plug is quite easily protected with a sticker, which breaks when the plug gets removed from the socket.

How to use USB keylogger - see video about it:
4. Hardware tab inside the system unit
Refer to the principle of action, this solution does not differ from the devices of types 1 and 3 but is located inside the system unit. It can be installed only by a specialist, and it will require opening the unit case.
Solution: system unit sealing using stickers. But before, it is necessary to inspect the system unit contents and make sure there are no unknown devices (typical connection place – the motherboard. Connection is parallel to the keyboard socket)
5. Information reading based on the analysis of acoustic and electromagnetic emitting
To catch keyboard electromagnetic emitting at a distance is difficult (although in theory, it is possible), but catching acoustic noise is much easier. Even when talking on the phone you can sometimes clearly hear your interlocutor typing on the keyboard. Studies in the security sphere show that each key, when pressed, produces a specific sound, which allows identifying the key. The most famous work in this area was made by UC Berkeley scientists, who came to the conclusion that in common audio recording from 60 to 96% of input characters can be recognized.
Without the use of specialized analysis software, you can simply detect the number of typed characters in a password and the presence of repeated characters.
Solution: the main way of protecting against information leakage by acoustic signals analysis is a continuous and systematic staff instructing.


 Español
Español Русский
Русский Deutsch
Deutsch Suomi
Suomi Français
Français Italiano
Italiano 日本語
日本語 Nederlands
Nederlands Português
Português Türkçe
Türkçe 中文
中文 عربي
عربي Tagalog
Tagalog اردو
اردو Gaeilge
Gaeilge বাংলা
বাংলা Magyar
Magyar Polski
Polski Čeština
Čeština Български
Български Bahasa Indonesia
Bahasa Indonesia 한국어
한국어 Română
Română Svenska
Svenska