Invisible Keylogger
2013-06-10
What Invisible Keylogger Can Do For YouSpyrix Personal Monitor has invisible keylogger system that is very essential in computing activities. This is because the system has been designed to perform analysis and monitoring in computer usage. Therefore, any problem that may arise resulting from improper usage of computers, the problem is quarantined before it erupts and results to serious damage. Due to this functionality the system has been employed in different places acting as a checker replacing supervision which is costly and sometimes difficult. Thanks to this system many issues are resolved before they reach out of hand to the point of being irreversible.
Invisible free keylogger has been designed to perform various activities. One of these activities is that it enables parents to know the amount of time kids spends on the internet. This is because education has shifted to digital mode where researches are conducted with the help of internet. At times kids claim that they are doing their research while in real sense they are browsing inappropriate site which corrupts their mind. With this system monitoring of the sites which your kids are browsing is made possible. Thus, parents have now the ability to determine the amount of time spent by their kids on the internet and in which site. The system is thus essential in ensuring that kids are properly raised.
In businesses and companies invisible keylogger is very important. This is because it helps to determine which sites employees visit during working hours. Performance in many companies have declined this is because a lot of time is wasted on social sites such as Facebook and Twitter. To combat these cases of time wastage this system come in handy as it reveals the sites which employees visit and the time spent on a particular site. With this system one is able to issue a warning to specific employees who are using working hours in social sites.
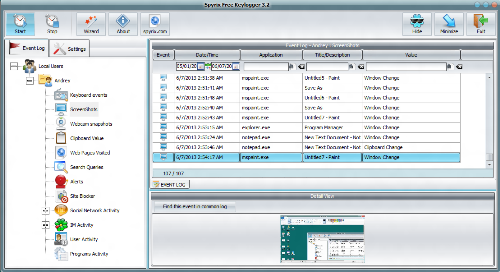
The invisible keylogger collects all the activities that occurred in each computer. After collection of these activities a report is produced. The report is easy to comprehend because it shows the keys which were pressed as well the websites which were visited. The system will even go to the extent of showing the information which was duplicated from the clipboard. Therefore, companies are unable to closely supervise their employees are advised to implement usage of this system. This is because monitoring of computer usage activities is undertaken undetected and thus employees are unable to hide.
The invisible keylogger from Spyrix Personal Monitor has been enhanced to an extent that employees using working hours in social sites are warned immediately they open a given social site. This system is very important particularly when one is unable to oversee activities which are undergoing in each computer due to absence or when occupied with other things. This is achieved through blacklisting some sites which send warning signals when employees open restricted sites in working hours. When the employees realize they are being monitored they strictly adhere to the rules and avoid contrary actions.


 Español
Español Русский
Русский Deutsch
Deutsch Suomi
Suomi Français
Français Italiano
Italiano 日本語
日本語 Nederlands
Nederlands Português
Português Türkçe
Türkçe 中文
中文 عربي
عربي Tagalog
Tagalog اردو
اردو Gaeilge
Gaeilge বাংলা
বাংলা Magyar
Magyar Polski
Polski Čeština
Čeština Български
Български Bahasa Indonesia
Bahasa Indonesia 한국어
한국어 Română
Română Svenska
Svenska