Top 5 Keylogger Software for Business and Family Needs
2026-02-19
Are keyloggers really a controversial concept, or are they legal anyway? Let's look at the top 5 keylogger software options that are primarily used for legal monitoring of company-owned devices and personal PCs.
Spyrix Keylogger Software for Windows, Mac, and Android
Spyrix is presented as a cross-platform monitoring tool designed to track and record digital activity. It's compatible with the following operational systems:
Such a combinability allows potential users to leverage this keystroke logger for different purposes. Android monitoring is preferably applied as a parental control tool that manages the device usage.
Windows keylogger is applicable for both business and personal needs. Why? Windows takes the leading share on the operational system market and is equal to 69,75% (ElectroIQ).
Key Features - What Spyrix Keylogger Delivers
- Input operations: Records typing in applications and browsers to provide a clear timeline of actions.
- Screenshot capturing: Takes screen recordings that can be reviewed on demand.
- Live viewing: Allows watching device activity in real-time.
- Activity dashboard: Aggregates all logs (keystrokes, app usage, clipboard contents) into a single, organized interface for a daily summary.
- Website blocker: Includes a feature to block unwanted websites directly.
Use Cases
| Scenario | How Spyrix is Meant to Help |
|---|---|
| Parental control | Monitor children's online interactions to help ensure their safety and promote digital balance, with the child's knowledge. |
| Employee monitoring | Gain an overview of activity on company devices to improve productivity and focus on outcomes, with employee consent. |
| Personal backup | For an individual, it can serve as a personal log of computer activity to recall past actions or recover lost information. |
Spyrix markets itself as a feature-rich monitoring tool that provides visibility into device activity. Its entire legal concept rests on the principles of ownership, transparency, and consent. Its main purpose is to protect kids from online threats and enhance productivity out of the business environment.
Syteca - Keylogger for Employee Monitoring Software
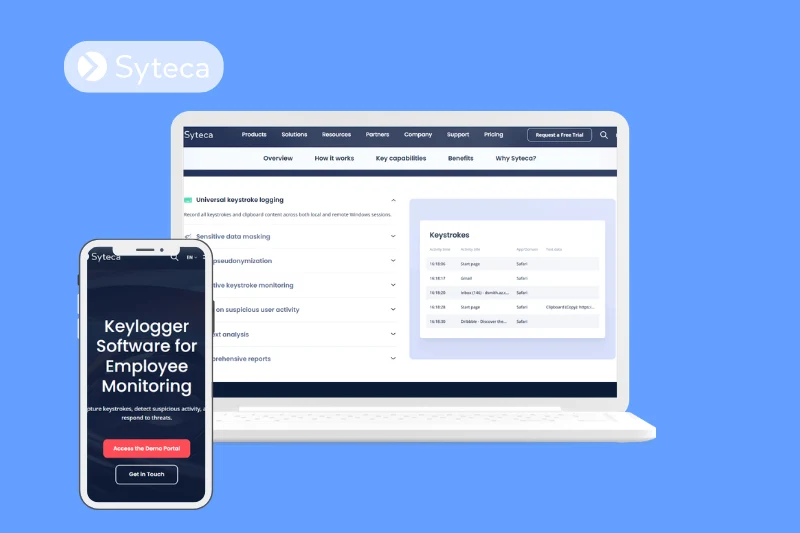
Syteca positions its keylogger not as a simple tracking tool, but as an integrated part of its User Activity Monitoring (UAM) solution. Its primary purpose is to enhance organizational security by providing deep, context-rich visibility into user actions to detect and respond to insider threats.
The software is designed for Windows PCs and servers. Once activated, it records keystrokes alongside on-screen activity in a video-like format, logging a comprehensive range of inputs:
- Character keys
- Modifiers (Shift, Ctrl, Alt)
- Navigation and typing mode keys
- System commands
- Function keys
It also tracks all clipboard actions, including copy, cut, and paste.
Key Capabilities of Syteca
| Capability | Description |
|---|---|
| Comprehensive recording | Logs all keystrokes and clipboard content in both local and remote Windows sessions. |
| Automated data masking | Intelligently hides sensitive data like passwords and credit card numbers in logs and live views to protect privacy. |
| Selective & triggered monitoring | Can limit logging to specific essential apps and initiate recording only when predefined keywords or clipboard actions occur. |
| Context-rich analysis | Aligns keystroke data with corresponding video fragments and other insights to show the full context of a user's session. |
| Real-time alerts & response | Sends alerts for suspicious keywords, allowing admins to respond instantly by displaying warnings, blocking users, or terminating processes. |
Syteca presents its keylogger software as a cybersecurity tool for organizations. It moves beyond simple monitoring to offer a system for detecting, understanding, and responding to insider threats, all while incorporating features designed to balance security needs with employee data privacy requirements.
Actual Keylogger: Comprehensive Computer Activity Monitoring
Actual Keylogger is a software solution designed to record and document all activity on a computer system. Positioned as a tool for obtaining a complete record of computer usage, it captures detailed data on user interactions for later review.
Key Features and Capabilities
According to its official website, Actual Keylogger provides a range of monitoring functions:
| Feature Category | Description |
|---|---|
| Keystroke recording | Captures all keyboard input, including typed messages and documents searched. |
| Screen activity capture | Takes periodic screenshots of the computer desktop to provide visual records of on-screen activity over time. |
| Application and file tracking | Logs which applications are launched and used, as well as files that are opened, modified, or transferred. |
| Clipboard monitoring | Records all text and data copied to the system clipboard. |
| Internet activity logging | Tracks websites visited, search queries performed, and time spent on various online platforms. |
| Stealth operation mode | The software can be configured to run in a hidden mode, making it undetectable to the computer user. |
| Automated report delivery | Collected logs and screenshots can be automatically delivered via email or uploaded to an FTP server at scheduled intervals. |
Compatibility and System Requirements
Actual Keylogger is developed for the Windows operating system. It is designed to be compatible with a wide range of Windows versions, including Windows 11, Windows 10, Windows 8, and Windows 7. The software is also available for macOS, suitable for OS X version 11 (Big Sur) and above.
Revealer Keylogger: Stealth Computer Activity Recorder
Revealer Keylogger is a software application for Windows designed to record all user activity on a computer. Marketed as a comprehensive monitoring tool, it operates in a hidden mode to capture keystrokes, screen activity, and more, with options for remote log delivery.
Key Features
| Feature Category | Description |
|---|---|
| Keystroke logging | Records all keyboard input, including passwords, conversations in social networks, and text typed in browsers' private (incognito) mode. |
| Screenshot capture | Automatically takes screenshots of the desktop or active application when the user types text or uses the mouse, providing visual activity records. |
| Remote monitoring | Delivers recorded logs and screenshots via email, Dropbox, Google Drive, OneDrive, FTP, or local network, with adjustable frequency from real-time to several times per day. |
| Invisible/stealth mode | Runs completely hidden in the background. The program does not appear in the Task Manager, taskbar, or the list of installed programs. |
| Password protection | The Pro version includes a feature to password-protect the program itself, preventing unauthorized users from accessing or disabling it. |
Compatibility
Revealer Keylogger is developed specifically for the Windows operating system. It is available for download as a "Revealer Keylogger Free 2026" version, indicating compatibility with modern Windows systems, including Windows 10 and likely Windows 11.
Best Free Keylogger - Multi-Purpose Computer Monitoring Tool
Best Free Keylogger is a software solution designed to monitor computer activity, marketed for use by parents, employers, system administrators, and schools. It operates by recording user actions on a Windows computer and providing detailed reports.
Key Features
| Feature Category | Specific Capabilities |
|---|---|
| Core activity logging | Records keystrokes, clipboard content, internet activity (including browser usage), and local application usage. |
| Screen capture | Takes periodic screenshots of on-going activities on the target computer. |
| Monitoring filters | Includes a "Smart Read" filter to make keystroke logs readable, advanced filtering, and options to limit monitoring by specific user or application. It also allows for scheduled monitoring. |
| Stealth & security | Operates in an invisible mode (undetectable by users and antivirus programs), uses password protection for access, and stores logs in encrypted files. |
| Report delivery | Can deliver reports via email, FTP, LAN, or automatically copy logs to a USB drive when plugged in. Reports are viewable in an HTML-based report viewer with search filters. |
| Management controls | Includes parental controls, web filtering, time limiting for internet access, and the ability to block specific applications or internet access entirely. Also features automatic log clearance and automatic uninstallation. |
Use Cases
The platform explicitly lists its target users as:
- Parents (for monitoring children's online activity)
- Businesses and System Administrators (for employee monitoring)
- Schools and Internet Cafes (for managing computer usage)
- Personal Users
Compatibility
The software is designed for the Windows operating system. The website notes its compatibility with all major browsers, including Firefox, Chrome, Opera, and Internet Explorer.
Summing Up
As this overview shows, keyloggers serve different purposes—from corporate security to parental control. The five solutions reviewed cater to distinct scenarios:
- For enterprise security and insider threat detection: Syteca leads with advanced features like data masking, real-time alerts, and compliance-focused monitoring.
- For cross-platform flexibility: Spyrix Keylogger works across Windows, Mac, and Android, making it suitable for both business use and transparent family monitoring.
- For comprehensive personal computer monitoring: Actual Keylogger and Revealer Keylogger offer robust activity logging with stealth options and remote report delivery across Windows and macOS.
- For granular control on Windows: Best Free Keylogger excels with extensive filtering, scheduling, and multiple delivery methods, ideal for system administrators and schools.
The right choice depends on your specific needs. However, the legal and ethical foundation remains the same across all options: use the software only on devices you own, with clear consent and transparency.

